July honeypot report
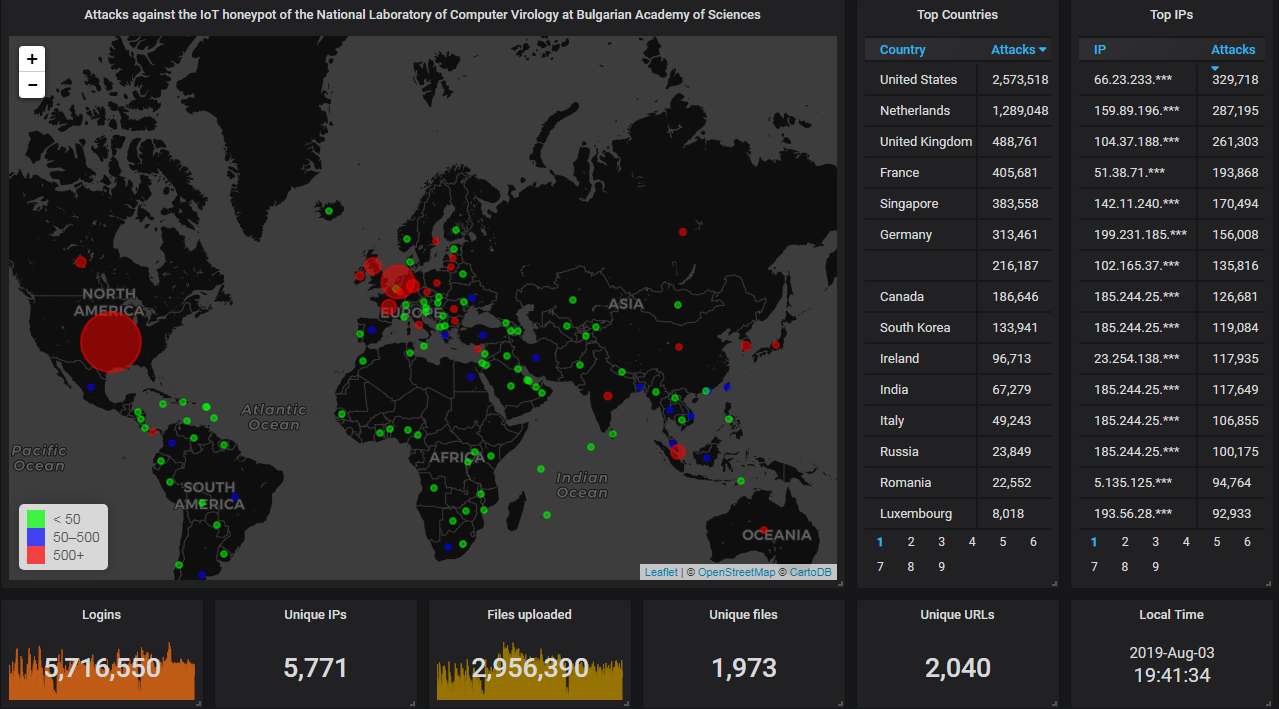
First, the data from our Telnet & SSH honeypot. The big picture looks like this. As usual, most attacks have come from the USA, with the Netherlands in the second place - again:
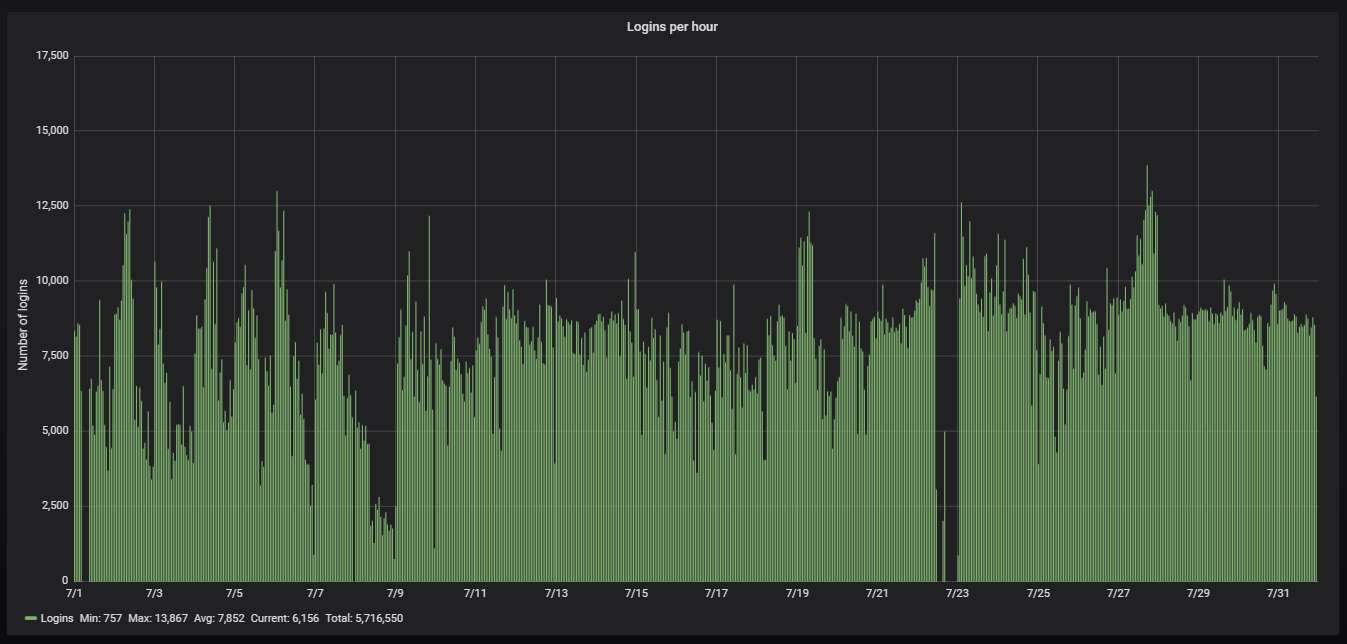
Here is how the hourly activity looks like. Slightly more than 2 attacks per second, as usual. The big gap is caused by an outage we had:
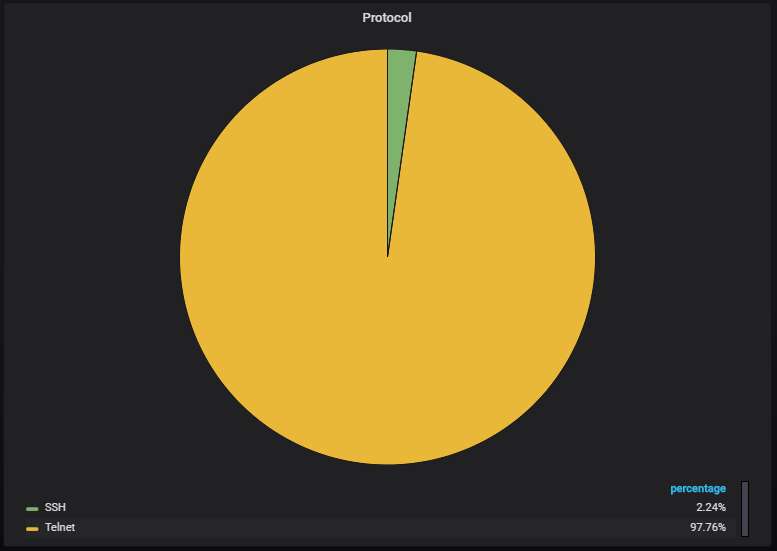
Nearly 98% of the attacks are via Telnet, the rest are via SSH. It seems that the Gafgyt botnet (which spreads via SSH) is slowly disappearing.
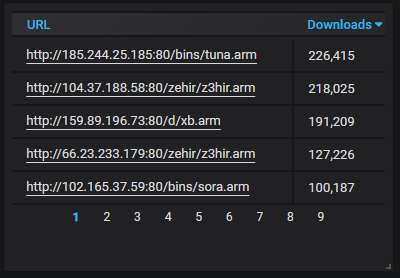
The top-5 URLs from which malware was most actively uploaded to the honeypot. Mirai variants all of them, as usual, although the original variant is not among them.
Details about the top-20 most actively attacking IPs. As usual, DigitalOcean is heavily present. The Dutch KV Solutions is even more heavily present than the last month. The the top spot is occupied by some US company I've never heard of, though:
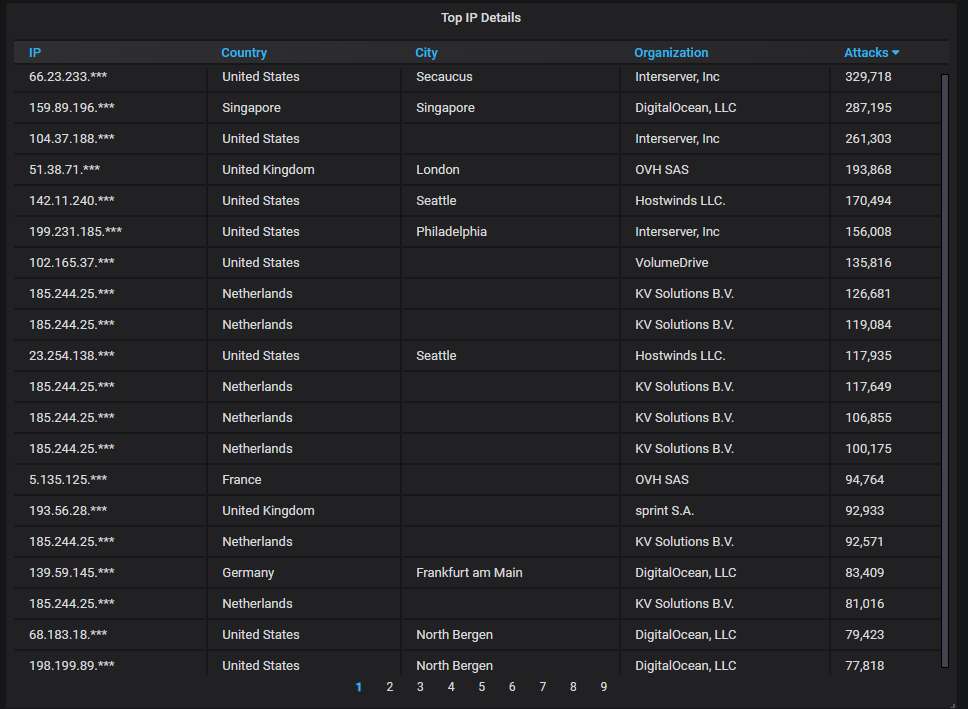
The top-20 most actively attacking organizations. DigitalOcean is at the top, as usual, but KV Solutions is relatively close behind:
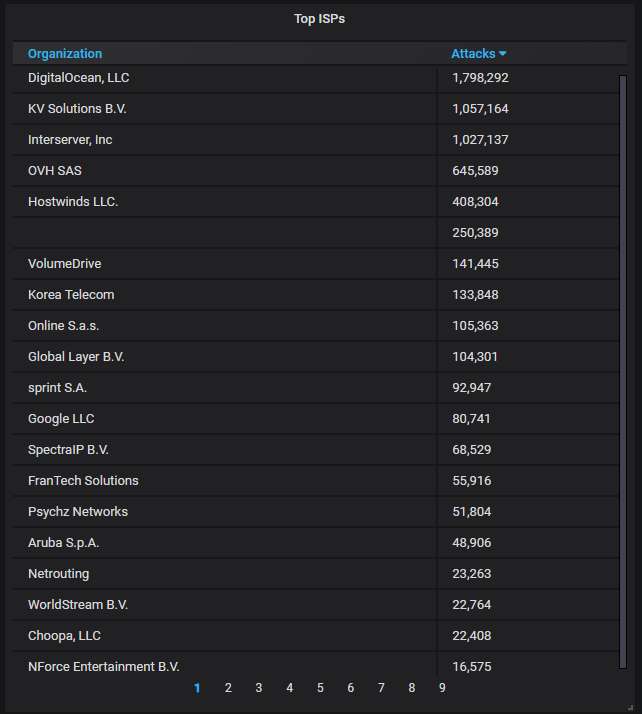
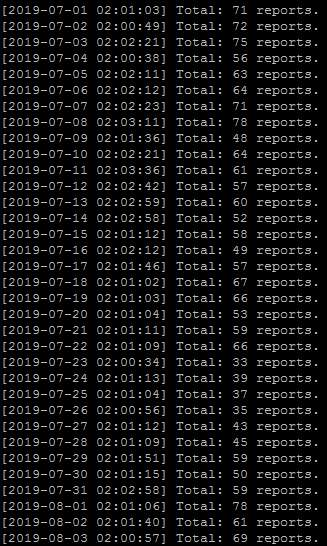
As you can see, I've been sending averagely nearly 60 automated abuse reports to DigitalOcean every day - but it doesn't seem to be helping very much.
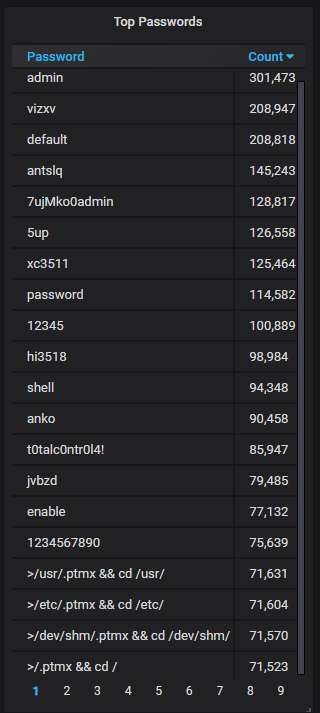
The top-20 passwords that are the most often used by the attackers; nothing unusual here:
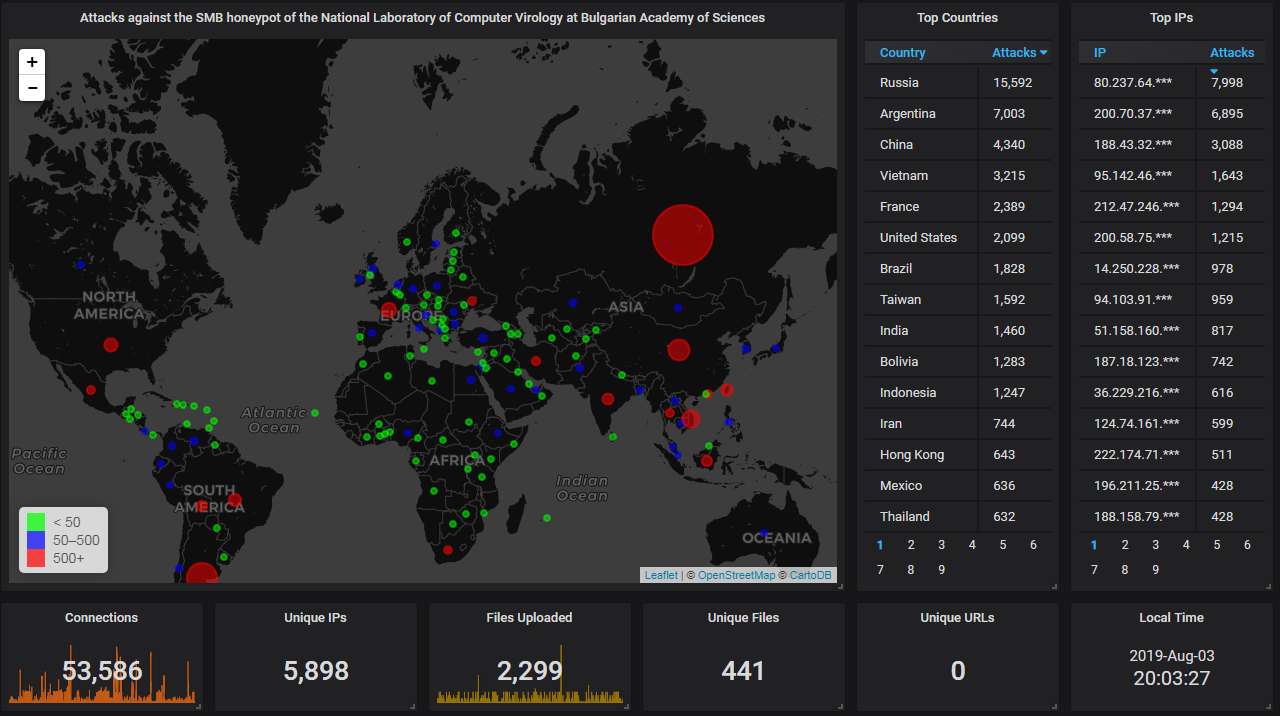
Moving on to our SMB honeypot.
First, the big picture. Russia not only holds the top spot but is also way ahead of everybody else:
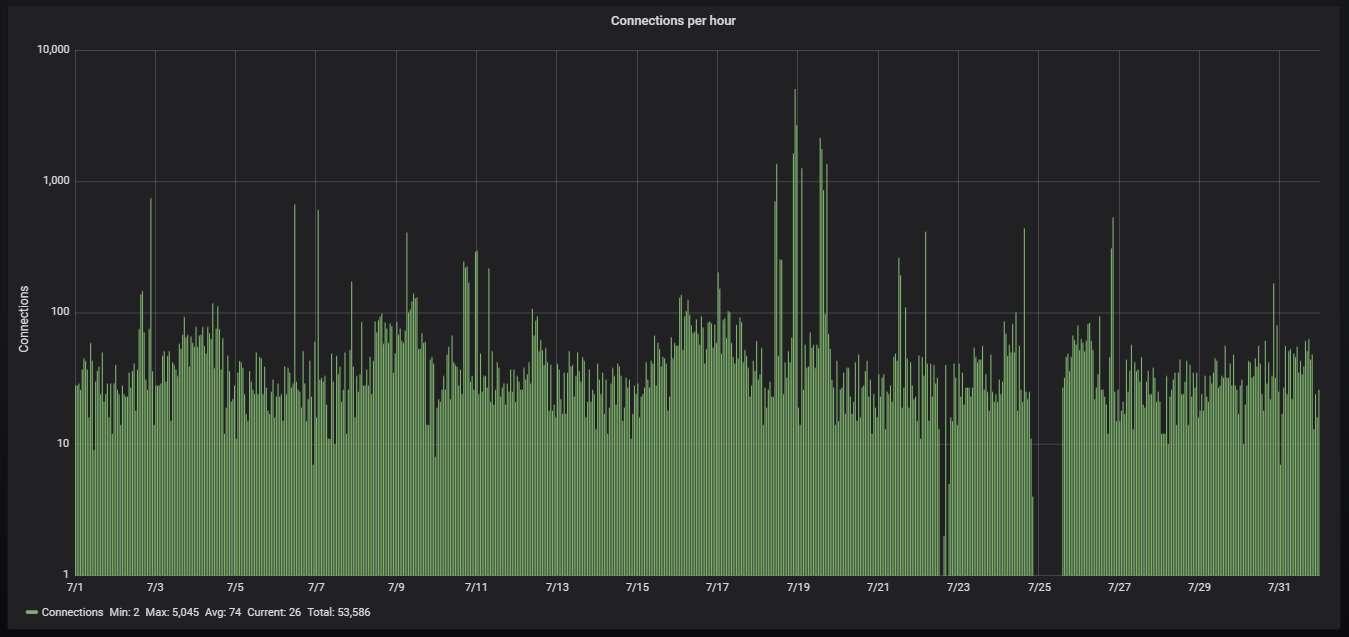
Hourly activity, showing averagely a bit more than one attack per minute. I've switched to a logarithmic scale, otherwise the lonely spikes of more than a thousand attacks coming from a single IP (usually infected with a WannaCry variant) tend to drown out everything else. Otherwise the traffic is pretty steady, albeit much lower than the one that the Telnet honeypot gets.
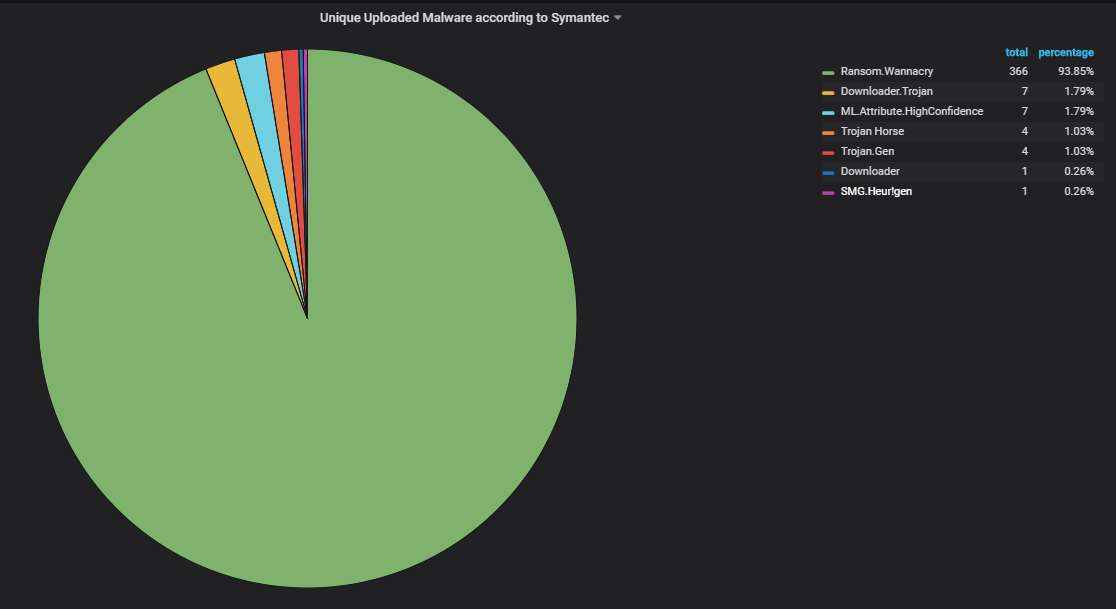
Unique uploaded malware variants, according to Symantec's scanner. Lots of corrupted WannaCry variants, as usual (no kill switch check, no encryption).
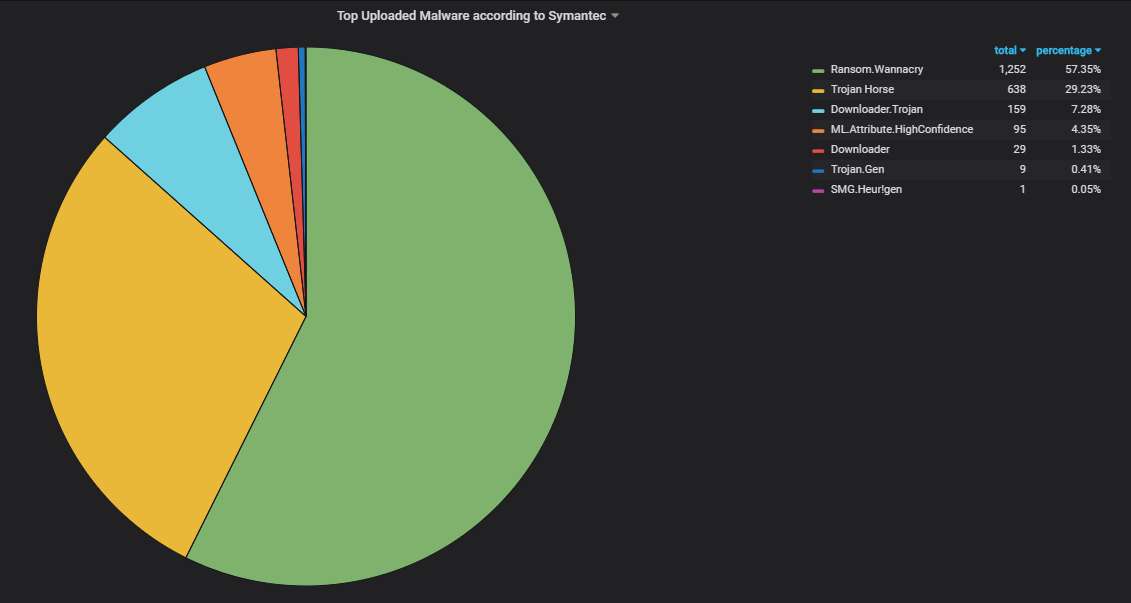
Note that WannaCry uploads dominate, although not as overwhelmingly, even if we don't count only the unique variants:
Details about the top-20 most actively attacking IPs. You can see why Russia is so heavily represented this month:
The top-20 organizations from which most of the attacks are coming from. Nothing unexpected here:
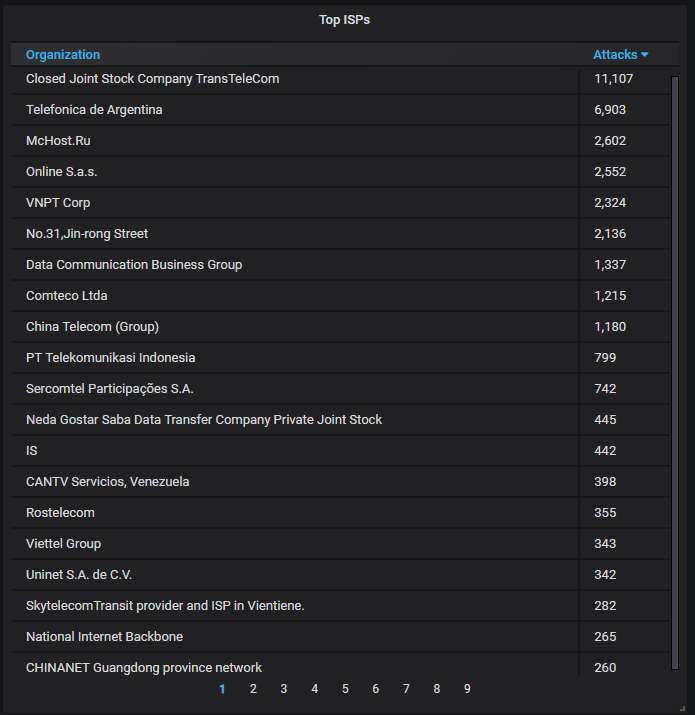
Finally, the data from our ADB honeypot.
The big picture shows that the usual suspects (China, Hong Kong, South Taiwan) seem to have a huge population of devices with the ADB port open to the Internet with no authentication. This month, however, the USA is also among the top offenders, even displacing South Korea, a previous "favorite":
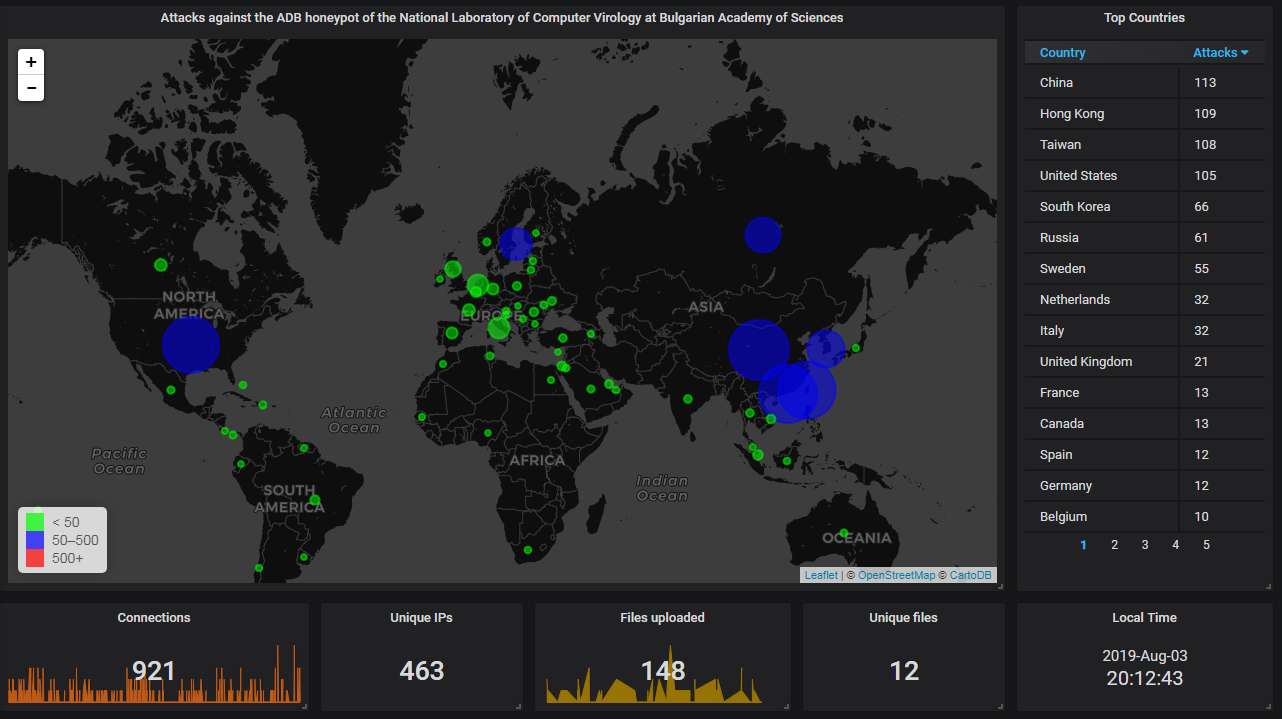
The hourly connection data, showing averagely slightly more than one attack every half an hour:
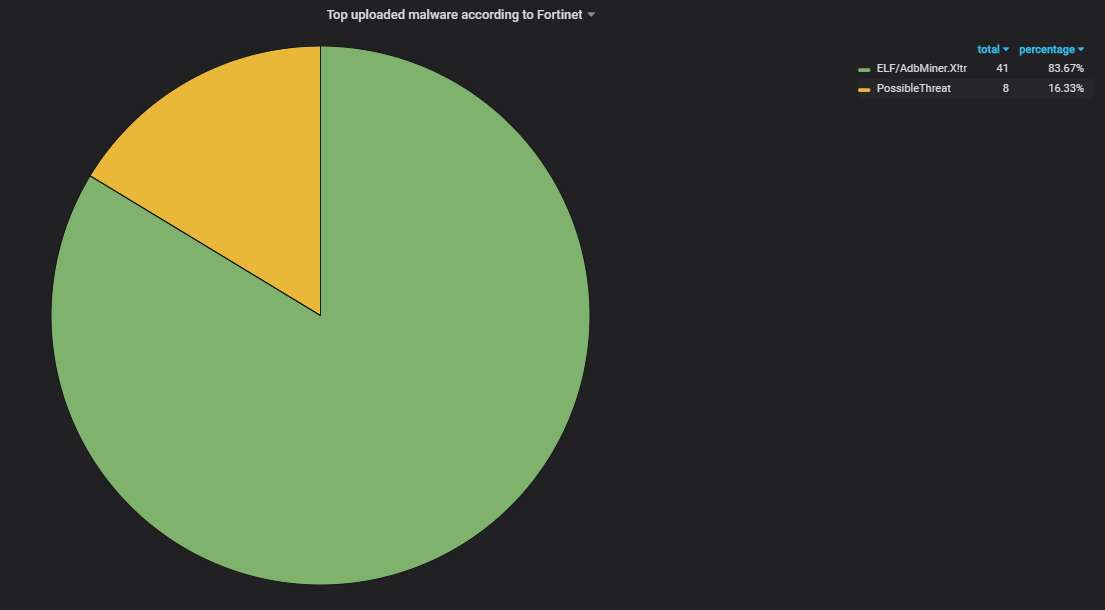
The malware uploaded to the honeypot, according to Fortinet's scanner. The same old Monero mining worm (Trinity) is causing most of the ADB traffic, plus something that is uploading a shell script that looks vaguely Mirai-like:
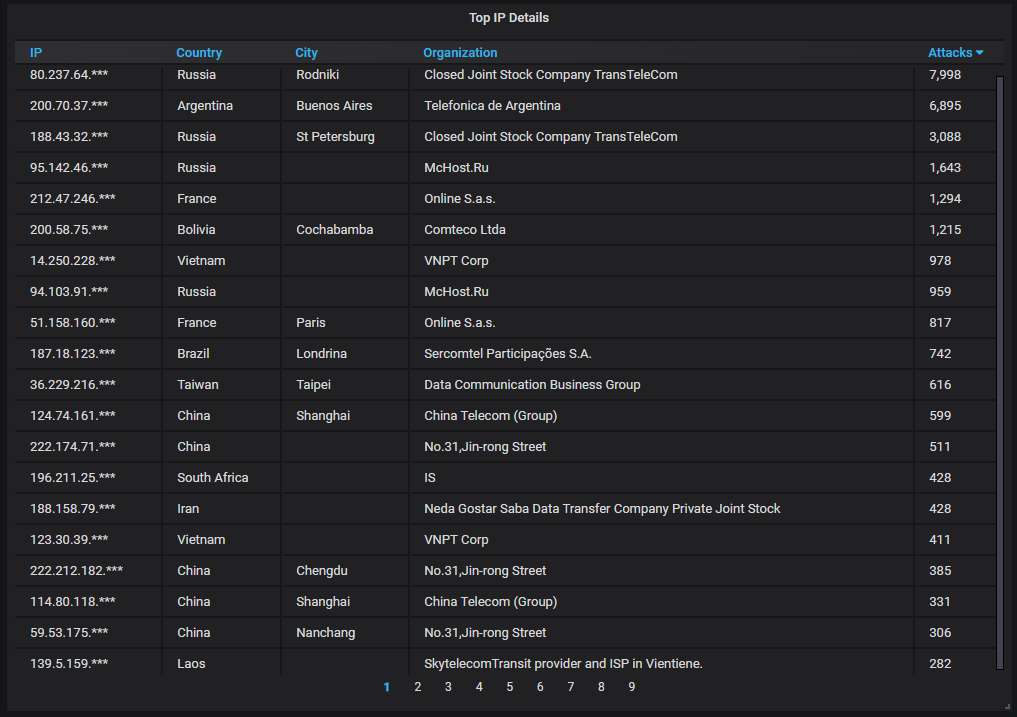
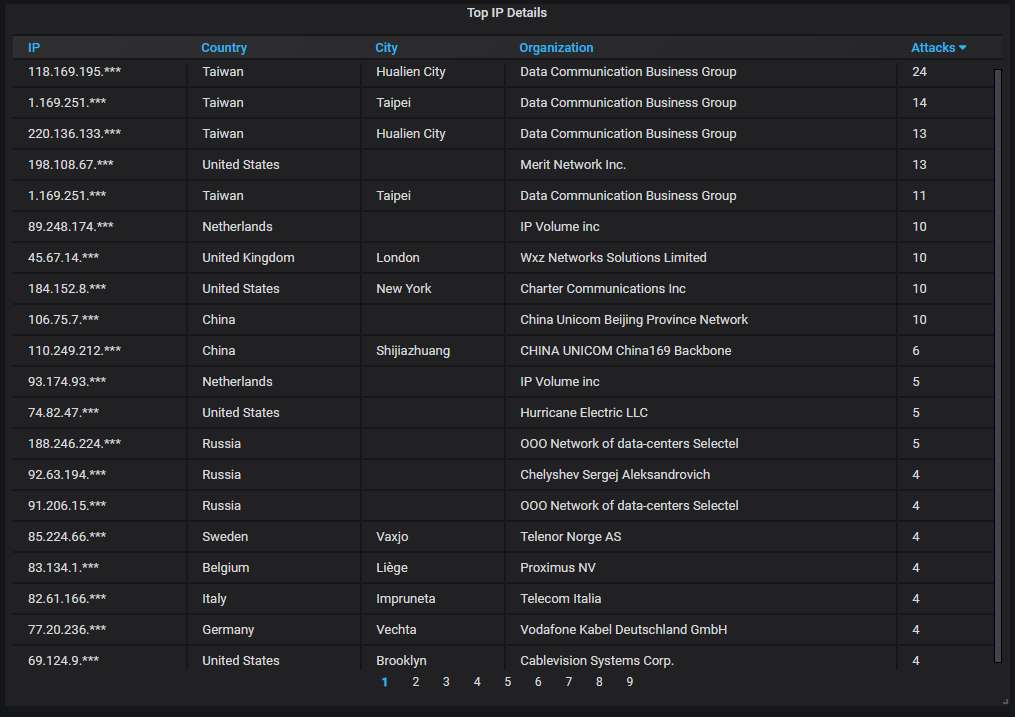
Details about the top-20 most actively attacking IPs. Nothing unusual here:
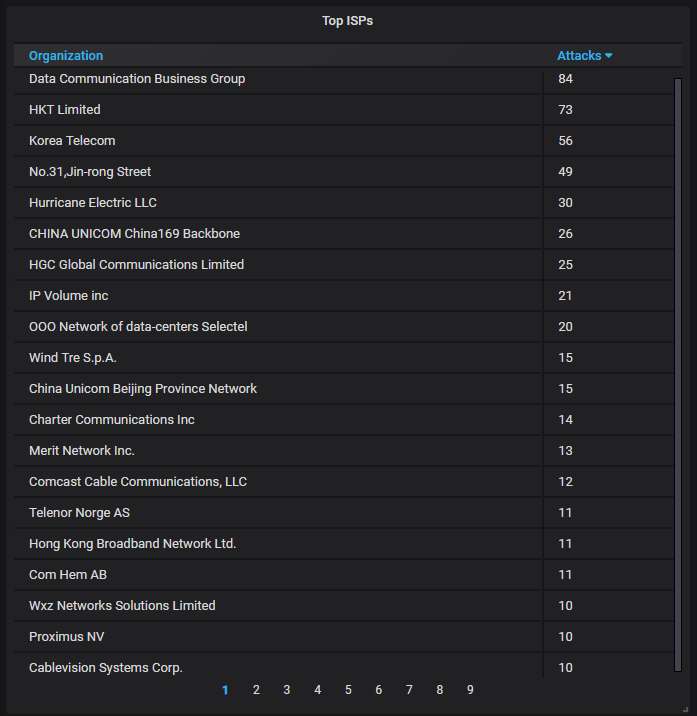
The top-20 organizations that own the IP addresses attacking us:
This concludes the July honeypot report.
